Investment Tips
24-04-2026 14:25
11 Views
A Guide to Honey-Pot Wallets: How to Trick Hackers into…
Key Takeaways
- Honey-pot wallets are designed to attract hackers and reveal their behavior.
- They help you track wallet addresses, actions, and common attack patterns.
- This approach turns passive security into a more active defense strategy.
- Blockchain transparency makes it easier to monitor and analyze suspicious activity.
- There is always a risk of losing funds placed inside the honeypot wallet.
- Proper setup and isolation are key to avoiding damage to real assets.
What is a Honey-Pot Wallet?
This refers to a crypto wallet that is created to resemble an easy target for hackers. It can appear poorly secured or contain visible funds. Its actual purpose is not to save money, but to attract attackers. The idea emanates from cybersecurity, where “honeypots” are used to lure hackers into fake systems, so their actions can be tracked. In crypto, the same idea is applied to smart contracts and wallets. Unlike a regular wallet that is meant to protect your funds, a honey-pot wallet is designed to be monitored. When someone tries to exploit or access it, you can monitor their behavior, track their wallet address, and understand how the attack works.Understanding How Honey-Pot Wallets Work
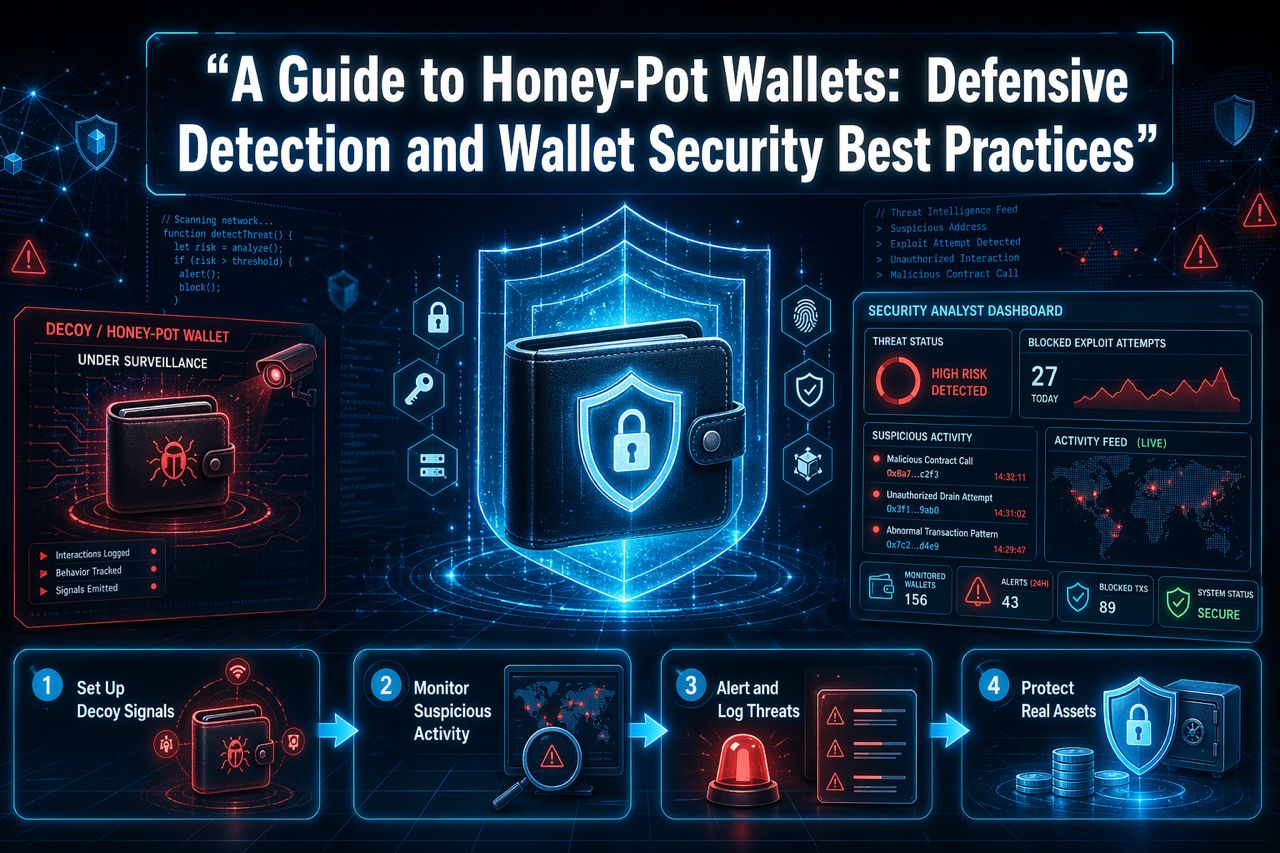
A honey-pot wallet functions by pretending to be an easy target. You create a separate wallet and set it up in a way that looks quite vulnerable, something that might capture a hacker’s attention. Next, you’ll add a minimal amount of crypto to make it look authentic and worth attacking. This bait is what attracts people in. From the outside, it resembles an actual wallet that hasn’t been properly secured. When someone tries to interact with it, that’s where its real purpose kicks in. You monitor the activity tracking things like transaction attempts, wallet addresses, and behavior patterns.How to Set Up a Honey-Pot Wallet
Here’s an easy way to set one up securely:1. Choose a Blockchain
Begin by selecting a network such as Ethereum, where transactions are public and easy to monitor. This makes it seamless to monitor wallet interactions and attacker behavior.2. Create a separate wallet
Always create a completely new wallet only for the honeypot. This prevents any accidental exposure of your personal crypto activity or real funds.3. Add small bait funds
Deposit a little funds of cryptocurrency to make the wallet look attractive and active. The objective is to draw attention without risking notable financial loss.4. Make it look slightly vulnerable
Present the wallet in a way that implies weak security, like poor practices or careless exposure. However, don’t compromise your sensitive information or real assets.5. Set up monitoring tools
Use wallet trackers, blockchain explorers, and alert systems to monitor all incoming and outgoing transactions. This will enable you to observe and record suspicious activity in real time.6. Keep it fully isolated
Ensure the wallet is totally separate from your main accounts, storage systems, and devices to prevent any chance of attackers gaining access to your real crypto holdings.Best Practices for Using Honey-Pot Wallets
Follow these practices to stay effective and safe:1. Use only what you can afford to lose
The funds in your honeypot should be treated as expendable. Always use a minimal amount you’re comfortable losing, since the wallet is designed to attract potential attackers.2. Don’t link to your main wallet
Ensure there’s no direct or indirect connection between your honeypot and your primary wallet. This includes addresses, shared devices, or transaction history that could expose your real assets.3. Monitor activity regularly
Check the wallet regularly or set automated alerts so you can promptly detect, analyze, and learn from any suspicious activity or attempted attacks.4. Update your setup over time
Hackers are constantly looking for ways to adapt. Therefore, you should occasionally modify your honeypot setup to keep it effective, realistic, and capable of attracting new attack methods.5. Don’t overcomplicate the trap
Ensure your setup is simple and believable. If the honeypot is too complex or unnatural, experienced attackers might recognize it as a trap and avoid interacting with it.6. Understand legal and ethical boundaries
Be aware of ethical considerations and local laws when using honeypots, especially when collecting data or monitoring behavior to avoid possible legal issues.Risks to Understand When Using Honey-Pot Wallets
While it can be useful, here are some real risks to look out for:1. Funds can be lost
Any crypto in the honeypot should be considered expendable because hackers can successfully withdraw it, especially when the setup isn’t properly controlled.2. Hackers may detect the trap
Expert attackers might sometimes recognize honeypots by identifying unusual setups or patterns. This means they can avoid it entirely or try to exploit it differently.3. Useful results aren’t guaranteed
Not every attacker interaction offers valuable insights. Some might use basic scripts or automated bots that don’t reveal much about actual attack strategies.4. Risk of misconfiguration
If the smart contract or wallet is poorly set up, you might accidentally expose more than intended. Worse still, vulnerabilities might be created that can affect other aspects of your crypto setup.Conclusion - Smarter Crypto Security Going Forward
Honey-pot wallets reveal that crypto security doesn’t have to be purely defensive. By setting controlled traps, you can learn how attackers think and improve your protection strategies over time. That said, this method should be used carefully. It works best as a learning and monitoring tool, not a guaranteed way to stop attacks. When used properly, these wallets can offer you valuable insights and a smarter edge in protecting your crypto assets.
Other news

24-04-2026 14:25

23-04-2026 14:24

